NIST’S FISMA Pase II–Who Certifies Those who Certify the Certifiers?
Posted June 17th, 2008 by rybolovCheck out this slideshow and this workshop paper from 2006 on some ideas that NIST and a fairly large advisory panel have put together about certification of C&A service providers. I’ve heard about this for several years now, and it’s been fairly much on a hiatus since 2006, but it’s starting to get some eartime lately.
The interesting thing to me is the big question of certifying companies v/s individuals. I think the endgame will involve doing both because you certify companies for methodology and you certify people for skills.
This is the problem with certification and accreditation services as I see it today:
- Security staffing shortage means lower priority: If you are an agency CISO and have 2 skilled people, where are you going to put them? Odds are, architecture, engineering, or some other high-payoff activity, meaning that C&A services are candidates for entry-level security staff.
- Centralized v/s project-specific funding: Some agencies have a “stable” of C&A staff, if it’s done wrong, you end up with standardization and complete compliance but not real risk management. The opposite of this is where all the C&A activities are done on a per-project basis and huge repetition of effort ensues. Basic management technique is to blend the 2 approaches.
- Crossover of personnel from “risk-avoidance” cultures: Taking people from compliance-centric roles such as legal and accounting and putting them into a risk-based culture is a sure recipe for failure, overspending, and frustration.
- Accreditation is somewhat broken: Not a new concept–teaching business owners about IT security risk is always hard to do, even more so when they have to sign off on the risk.
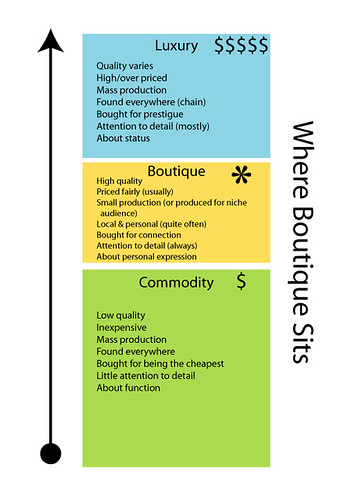
- C&A services are a commodity market: I covered this last week. This is pivotal, remember it for later.
- Misinformation abounds: Because the NIST Risk Management Framework evolves so rapidly, what’s valid today is not the same that will be valid in 2 years.
So what we’re looking at with this blog post is how would a program to certify the C&A service providers look like. NIST has 3 viable options:
- Use Existing Certs: Require basic certification levels for role descriptions. DoD 8570.1M follows this approach. Individual-level certification would be CAP, CISSP, CG.*, CISA, etc. The company-level certification would be something like ITIL or CMMI.
- Second-Party Credentialing: The industry creates a new certification program to satisfy NIST’s need without any input from NIST. Part of this has already happened with some of the certifications like CAP.
- NIST-Sponsored Certification: NIST becomes the “owner” of the certification and commissions organizations to test each other.
Now just like DoD 8570.1M, I’m torn on this issue. On one hand, it means that you’ll get a higher caliber of person performing services because they have to meet some kind of minimum standard. On the other hand, introducing scarcity means that there will be even less people available to do the job. But the big problem that I have is that if you introduce higher requirements on commodity services, you’re squeezing the market severely: costs as a customer go up for basic services, vendors get even less of a margin on services, more charlatans show up because you’ve tipped over into higher-priced boutique services, and mayhem ensues.
Guys, I’m not really a rocket scientist on this, but really after all this effort, it seems to me that the #1 problem that the Government has is a lack of skilled people. Yes, certifying people is a good thing because it helps weed out the dirtballs with a very rough sieve, but I get the feeling that maybe what we should be doing instead is trying to create more people with the skills we need. Alas, that’s a future blog post….
However, the last thing that I want to see happen is a meta-game of what’s going on with certifications right now–who certifies those who certify? I think it’s a vicious cycle of cross-certification that will end up with the entire Government security industry becoming one huge self-licking ice cream cone. =)
Similar Posts:
Posted in FISMA, NIST, What Doesn't Work, What Works |  3 Comments »
3 Comments »
Tags: accounting • auditor • cashcows • compliance • fisma • government • infosec • management • moneymoneymoney • risk • scalability • security
 Posts RSS
Posts RSS