OK, I know you’re shocked…I’m saying something controversial. But hear me out on this one, I’ll explain.
Now this is my major beef with the way we write SSPs today: this is all information that is contained in other artifacts that I have to pay people to do cut-and-paste to get it into a SSP template. As practiced, we seriously have a problem with polyinstantiation of data in various lifecycle artifacts that is cut-and-pasted into an SSP. Every time you change the upstream document, you create a difference between that document and the SSP.
This is a practice I would like to change, but I can’t do it all by myself.
This is the skeleton outline of an SSP from Special Publication 800-18, the guide to writing an SSP:
- Information System Name/Title–On the investment/FISMA inventory, the Exhibit 300/53, etc
- Information System Categorization–usually on a FIPS-199 memorandum
- Information System Owner–In an assignment memo
- Authorizing Official–In an assignment memo
- Other Designated Contacts–In an assignment memo
- Assignment of Security Responsibility–In assignment memos
- Information System Operational Status–On the investment/FISMA inventory, the Exhibit 300/53, etc
- Information System Type–On the investment/FISMA inventory, the Exhibit 300/53, etc
- General System Description/Purpose–In the design document, Exhibit 300/53
- System Environment–Common controls not inside the scope of our system
- System Interconnections/Information Sharing–from Interconnection Security Agreements
- Related Laws/Regulations/Policies–Should be part of the system categorization but hardly ever is on templates
- Minimum Security Controls–800-53 controls descriptions which can easily be done in a Requirements Traceability Matrix
- Information System Security Plan Completion Date–specific to each document
- Information System Security Plan Approval Date–specific to each document
Now some of this has changed in practice a little bit–# 10 can functionally be replaced with a designation of common controls and hybrid controls.
So my line of thinking is that if we provide a 2-6-page system description with the names of the “guilty parties” and some inventory information, controls-specific Requirements Traceability Matrix, and a System Design Document, then we have the functional equivalent of an SSP.
Why have I declared an InfoSec fatwah against SSPs as currently practiced?
Well, my philosophy for operation is based on some concepts I’ve picked up through the years:
- Why run when you can walk, why walk when you can sit, why sit when you can lay down. There is a time to spend effort on determining what the security controls are for a project. You need to have them documented but it’s not cost-effective to be worried about format, which we do probably too much of today.
- Make it easy to do the right thing. If we polyinstantiate security information, we have made something harder to maintain. Easier to maintain means that it will get maintained instead of being shelfware. I would rather have updated and accurate security information than overly verbose and well-polished documents that are inaccurate.
- Security is not a “security guy thing”–most problems are actually a management and project team problem. My idea uses their SDLC artifacts instead of security-specific versions of artifacts. My idea puts the project problems back in the project space where it belongs.
- If I have a security engineer who has a finite amount of hours in a day, I have to choose what they spend their time on. If it’s a matter of vulnerability mitigation, patching, etc, or correcting SSP grammar, I know what I want him to do. Then again, I’m still an infantryman deep down inside and I realize I have biases against flowery writing.
Criticisms to not writing a dedicated SSP document:
“My auditors are used to seeing the information in the same format at someplace they worked previously”. Believe it or not, I hear this quite a bit. My response is along the lines of the fact that if you make your standard be what I’m suggesting for a security plan, then you’ve met all of the FISMA and 800-53 requirements and my personal requirement to “don’t do stupid stuff if you can help it”.
“My auditors will grill me to death if they have to page back and forth between several documents”. This one also I’ve heard. There are a couple of ways to deal with this. One way to deal with this is that in your 800-53 Requirements Traceability Matrix you reference the source document. Most auditors at this point bring up that you need to reference the official name, date of publication, and specific page/section of the reference and I think they need to get a life because they’ve taken us back to the maintainability problem.
“This is all too new-school and I can’t get over it”. Then you are a dinosaur and your kind deserves extinction. =)
.
This blog post is for grecs at novainfosecportal.com who perked up instantly when I mentioned the concept months ago. Finally got around to putting the text somewhere.
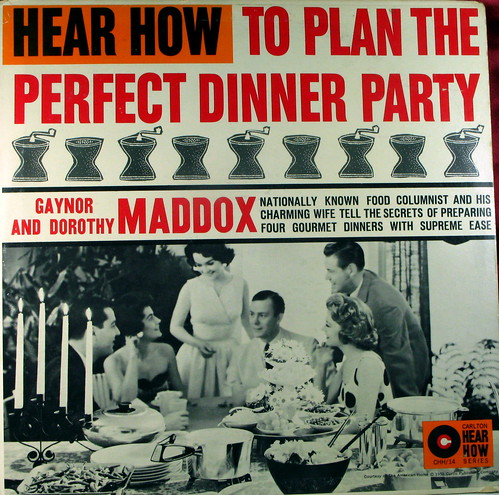
How to Plan the Perfect Dinner Party photo by kevindooley.
Similar Posts:
 6 Comments »
6 Comments » Posts RSS
Posts RSS