Posted December 13th, 2009 by
rybolov
A small presentation Dan Philpott and I put together for Potomac Forum about getting sane social media policy out of your security staff. I also recommend reading something I put out a couple of months ago about Social Media Threats and Web 2.0.
Similar Posts:
Posted in FISMA, NIST, Outsourcing, Risk Management, Speaking |  4 Comments »
4 Comments »
Tags: 800-53 • accreditation • catalogofcontrols • certification • compliance • fisma • gov20 • government • infosec • infosharing • itsatrap • management • NIST • omb • risk • scalability • speaking
Posted December 1st, 2009 by
rybolov
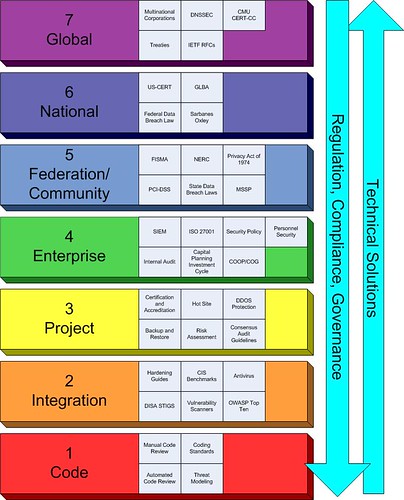
OK, so it’s been a couple of months of thinking about this thing. I threw together a rainbow-looking beast that now occupies my spare brain cycles.
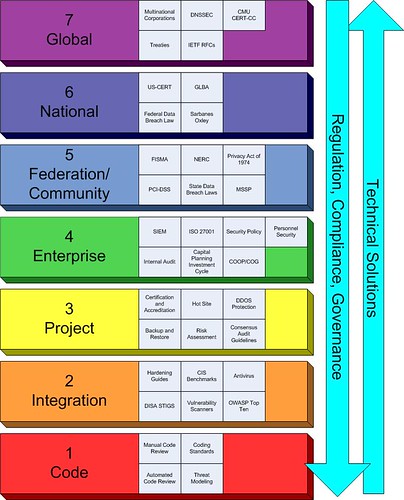
Rybolov’s Information Security Management Model
And some peculiarities of the model that I’ve noticed:
Regulation, Compliance, and Governance flows from the top to the bottom. Technical solutions flow from the bottom to the top.
The Enterprise (Layer 4) gets the squeeze. But you CISOs out there knew that already, right? It makes much sense in the typical information security world to focus on layers 3, 4, and 5 because you don’t usually own the top and the bottom of the management stack.
The security game is changing because of legislation at layers 5 and 6. Think national data breach law. It seems like the trend lately is to throw legislation at the problems with information security. The scary part to me is that they’re trying to take concepts that work at layers 3 and 4 and scale them up the model with very mixed results because there isn’t anybody doing studies at what happens above the Enterprise. Seriously here, we’re making legislation based on analogies.
Typically each layer only knows about the layer above and below it. This is a serious problem when you have people at layers 5 and 6 trying to create solutions that carry down to layers 1 through 4.
At layers 1 and 2, you have the greatest chance to solve the root causes of security problems. The big question here is “How do we get the people working at these layers the support that they need?”
Similar Posts:
Posted in Public Policy |  7 Comments »
7 Comments »
Tags: government • infosec • legislation • management • publicpolicy • scalability • security
Posted November 7th, 2009 by
rybolov
For those of you who didn’t know the real purpose of DojoCon, it was to raise money and awareness for Hackers for Charity. If you like anything that is in this post, go to HFC and make a donation of time, equipment, tech support, and maybe money. If you’ve never heard of HFC because you’re not one of the “InfoSec Cool Kids”, now is your chance–go read about them.
The video of my dojocon presentation. The microphone was off for the first couple of minutes but I look pretty animated.
And then the compliance panel that I tried not to dominate:
And finally, my slides are up on slideshare:
Similar Posts:
Posted in FISMA, Speaking |  6 Comments »
6 Comments »
Tags: 800-53 • accreditation • auditor • C&A • catalogofcontrols • certification • compliance • fisma • government • infosec • itsatrap • management • scalability • security • speaking
Posted November 2nd, 2009 by
rybolov
So I’m working with the AppSecDC folks doing press relations amongst other things. I’ve noticed several themes for the conference that might be of interest to the rest of the world. Of course there’s the usual “The end is nigh, and not even Norton can save you!!!!!” stuff that’s been the staple of security conferences for the past 5 years or so (oh noes, teh Internetz are broken. Again)
However, AppSecDC has another set of themes that are mostly unique to OWASP and AppSecDC in particular:
- The OWASP Approach to Security: it’s not process/product, it’s education and outreach. Thanks to Doug Wilson for this idea. Basically with host and network security, the option is to buy stuff and throw it at the problem. With application security, it’s “go out and touch a developer today” and “use ESAPI as a tool to help the developers write better and secure code more quickly”. This is a new concept to the system integrator that I am, but I like it much better than my usual approach.
- Government and Application Security: we’re about 5 years behind industry, how do we catch up? To this effort, we have some notable Government speakers such as a keynote by Joe Jarzombek, Director for Software Assurance in the National Cyber Security Division of the U.S. Department of Homeland Security.
- OWASP Top 10 2009/2010: This will be announced at AppSecDC with much w00tness and excitement.
- OWASP National Summit: this will be held the day before the official conference.
Convinced you want to go? Check out the conference site.
Similar Posts:
Posted in Odds-n-Sods, What Works |  1 Comment »
1 Comment »
Tags: government • infosec • management • owasp • security
Posted October 16th, 2009 by
rybolov
My presentation slides from Sector 2009. This was a really fun conference, the Ontario people are really, really nice.
Presentation Abstract:
The US Federal Government is the world’s largest consumer of IT products and, by extension, one of the largest consumers of IT security products and services. This talk covers some of the problems with security on such a massive scale; how and why some technical, operational, and managerial solutions are working or not working; and how these lessons can be applied to smaller-scale security environments.
Similar Posts:
Posted in FISMA, NIST, Public Policy, Speaking, The Guerilla CISO, What Works |  No Comments »
No Comments »
Tags: catalogofcontrols • certification • compliance • fisma • government • infosec • infosharing • law • legislation • management • publicpolicy • scalability • scap • security • speaking
 4 Comments »
4 Comments » Posts RSS
Posts RSS