Oh Hey, Secure DNS now Mandatory
Posted August 27th, 2008 by rybolovOMB sneaked this one in on me: OMB Memo 08-23 requires secure DNS (standard .pdf caveat). Agencies need to submit a plan by September 5th on how they should accomplish this. The whole switchover should occur by December 2009.
The interesting thing to me is that OMB is getting bolder in specifying technical solutions. Part of me wants to scream because public policy people have no business dictating technical solutions–that’s what we have standards boards and RFCs for.
From what I hear, some of this is because OMB is starting to be a really bad lame duck. Think about it, what are the odds that anybody at OMB is going to be around in December 2009? Completely unofficial word on the street is that OMB is pushing last-minute initiatives because of politicals–trying to accomplish things in time for the elections.
Also, I think that OMB is getting tired of NIST’s nonpspecificity in their guidance. NIST’s approach to being generic in nature is necessary because of their role as a research organization and the producers of methodologies.
The solution to all this? Well, the way it happens in the rational world is organic standards boards. Yes, they have their problems (*cough* WAFs anyone? *cough*) but overall, they fill a place. Inside Government, we don’t have much of that happening–we have the CIO council and the Enterprise Architecture folks, but nothing security-specific.
Lock Up Your Data photo by psd.
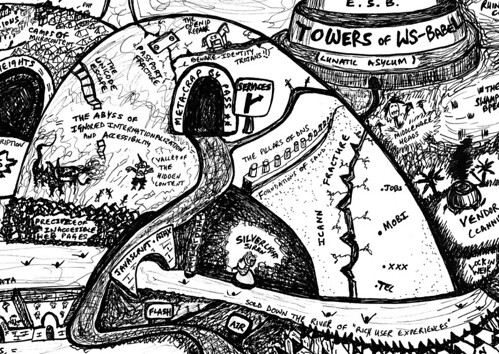
Description of the picture, it’s great and needs to be repeated:
The road passes the temptations of Flash and AIR. Those who succumb or who are unfortunate enough to be lured by Silverlight’s Siren find themselves sold down the river of Rich User Experiences and hurled towards lock-in weir. The TiddlyWiki steps may rescue some, who can then join those who stuck to the main path of Javascript and AJAX for their interactions.
The URI scheme is based on DNS, a registry which has weaknesses, meanwhile the ICANN Fracture results from their greedily adding spurious new Top Level Domains such as .mobi, .jobs, .xxx and even .tel, which whilst generating more revenue (for them) causes mass confusion and threatens to break the opacity of URIs.
Similar Posts:
Posted in Technical |  2 Comments »
2 Comments »
Tags: 800-53 • government • infosec • management • omb • security
 Posts RSS
Posts RSS

